3
Validate
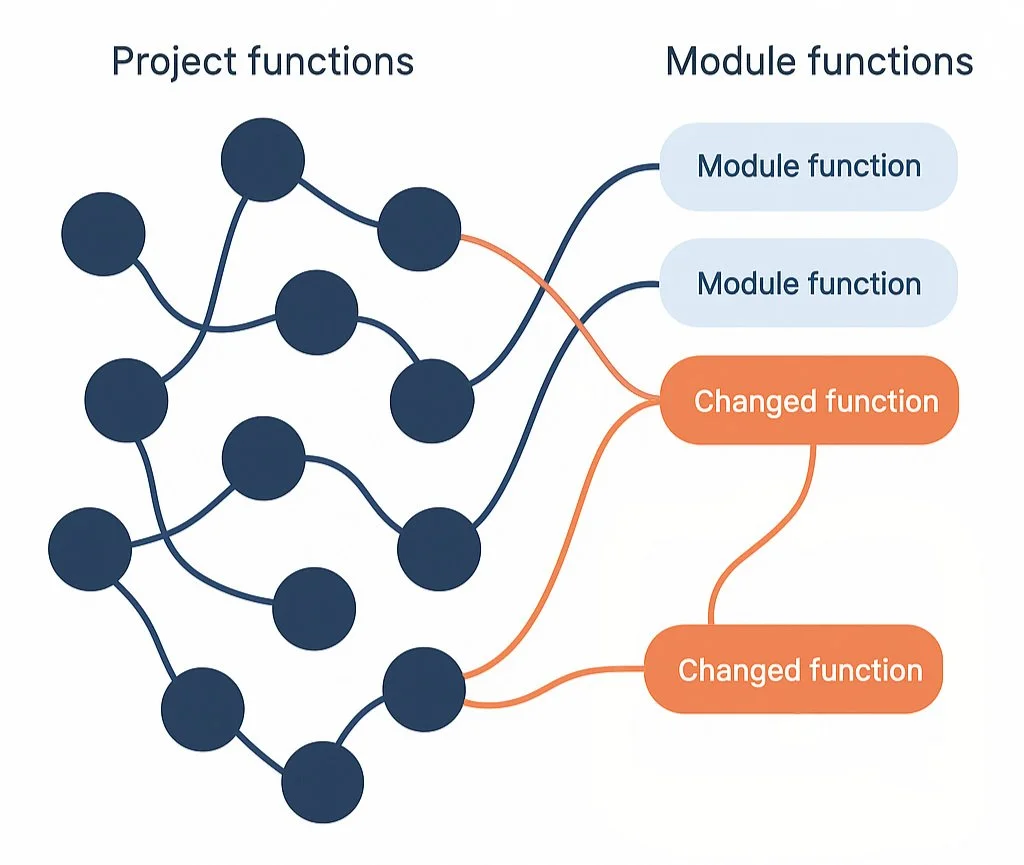
Once prepared, our tool is aware of the intersection from the dependency change and the project. We must then validate:
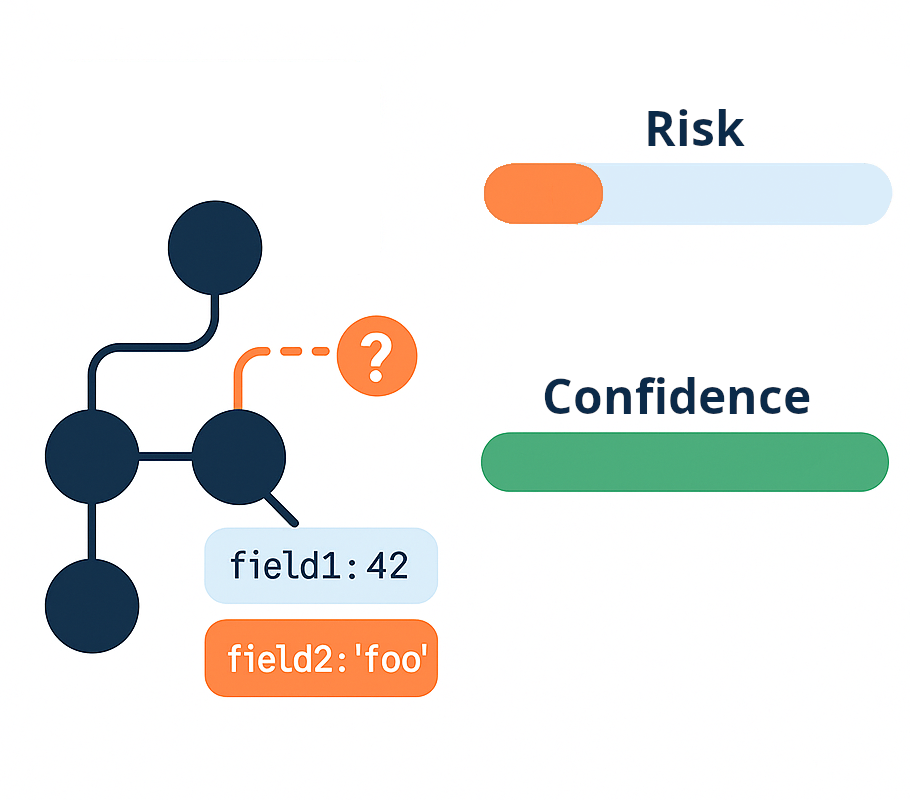
- Are there obvious test failures to consider — if so, we try to detect where the behavior change started
- At points where the project intersects a call path to a changed module function, are there any internal field or behavior changes
- The confidence that the tool was able to validate that behavior change
Risk is determined by performing a combination of unit testing and the field analysis described in the expand section above.
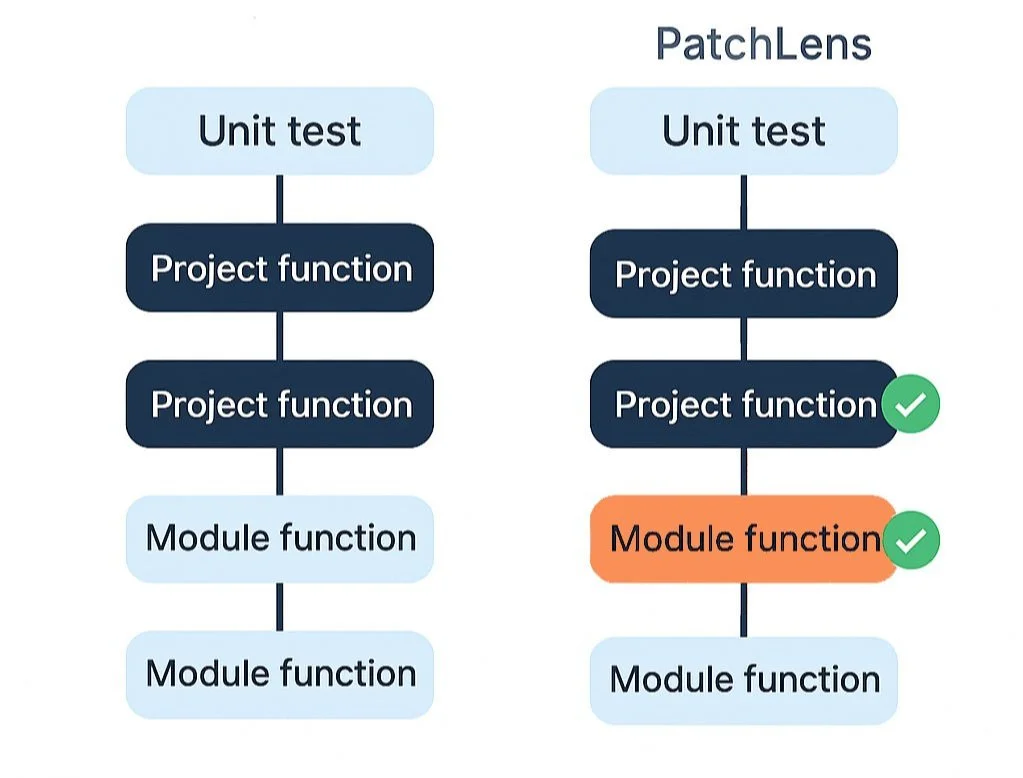
We determine confidence by:
- Validating that the expanded test suite reaches the targeted change points
- Introducing synthetic bugs at the logic changes within the dependency to confirm the tests can detect them
Beyond functional validation, PatchLens specifically elevates security concerns by monitoring how dependencies interact with security-sensitive operations. Even when code accessing sensitive resources isn't new, we flag any behavioral changes — like a networking library suddenly connecting to unexpected servers, or a utility attempting to access credential files. This runtime analysis helps detect zero-day supply chain attacks where malicious actors subtly alter legitimate package behavior to exfiltrate data or compromise systems.